Introduction
At Öruggt Net, we live and breathe cybersecurity. It is our specialty, and we are constantly learning, testing new things, and updating our knowledge. We believe it is our duty to stay well-informed so that we can potentially anticipate the actions of hackers.
When hackers launch an attack, they have usually spent a long time preparing for the attack itself. This is a well-known methodology used by burglars and terrorists, for example. They scout their target over a certain period and plan meticulously. In the context of terrorism, many organizations worldwide utilize counter-intelligence, known as “surveillance detection”. Specially trained personnel monitor movements around facilities and headquarters, hoping to spy on the spies and prepare for or prevent the attack.
Canaries
We came across a very clever solution that is available to everyone for free. This solution works much like real-world counter-intelligence and is called “Thinkst Canarytokens“. The name is historically fitting; in the past, canaries were used to warn miners if carbon monoxide levels in the mine became dangerous. These “canaries” work in a similar way, as they alert you to suspicious activity on your systems or other databases you are connected to. You create, configure, download, and deploy the “canaries” onto your systems (hardware, virtual, or cloud-based). You can set one up as a server, another as a router, a third as a credit card, and even one as a mobile app. These “birds” host services that look and behave exactly like genuine services but are actually decoys. You simply place them on your systems and leave them be.
Example
If or when hackers gain access somewhere and encounter your “birds” and start tampering with them, you will receive a notification that someone is interacting with something they shouldn’t be. See screenshot:
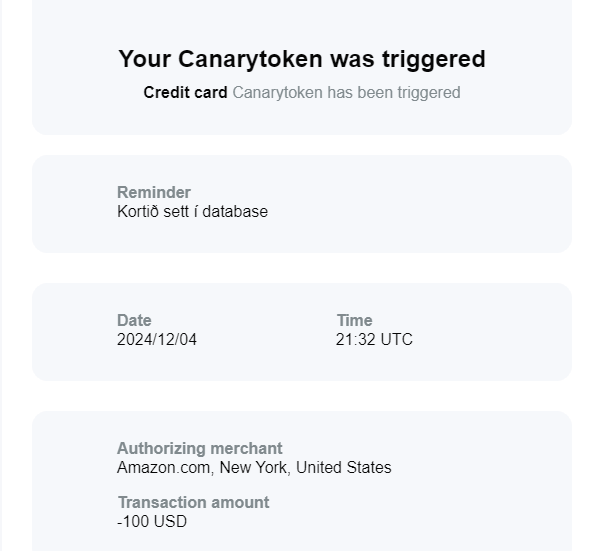
Here you can see how an unauthorized party had accessed a database where this “canary,” this decoy credit card, was stored. Appropriate measures can then be taken and further investigated. These are essentially “traps” set up in various places to alert you to suspicious “movements” so that you can respond before a major attack occurs.
In conclusion
Canarytokens is therefore a free tool that helps you know if you have been breached by letting the attackers expose themselves. You set up traps on your networks and receive a notification if someone falls into the trap, allowing you to take appropriate action.


